Identity Management historically has been a daunting task for many organizations. Now with cloud computing and services such as Office365, organizations are presented with new challenges. These challenges being synchronization of their user accounts, ensuring compliance as well as deactivating accounts in a timely fashion to reduce security risks.
Employees that leave the company may not have access to the corporate network, but they may have access to the cloud services such as Office365 at a given point. Companies must ensure disabling said account in a timely fashion.
Recently I’ve had great conversations with a few clients, our focal topic being Identity Management and what options are available to make this as painless as possible. For clients that use Office365 cloud services, there is almost always a need to sync their user accounts with O365. Not doing this correctly can lead to security risk or exposure.
So what options do organizations have for Active Directory User Account synchronization? Typically organizations will choose the following two options. Most small organizations may opt to have Office365 completely manage their accounts.

Directory Sync Tool With Password Sync
The Directory Sync tool which syncs your active directory objects to Azure AD within Office 365 and the password sync which retrieves your password hash from active directory and sync’s it to Azure AD. When both of these tools are used it makes it possible for users to keep the same password in their local domain as well as Office 365. The Directory Sync Tool is flexible in that you have the option to sync your entire directory or only a portion of your active directory, a particular OU for that matter.- Requires at least one server running DirSync Tool
- No SSO is possible with this option
- Credentials are managed on-premise.
- If account is disabled or deleted, Office365 will also delete or disable said account
</div> </div> </div>
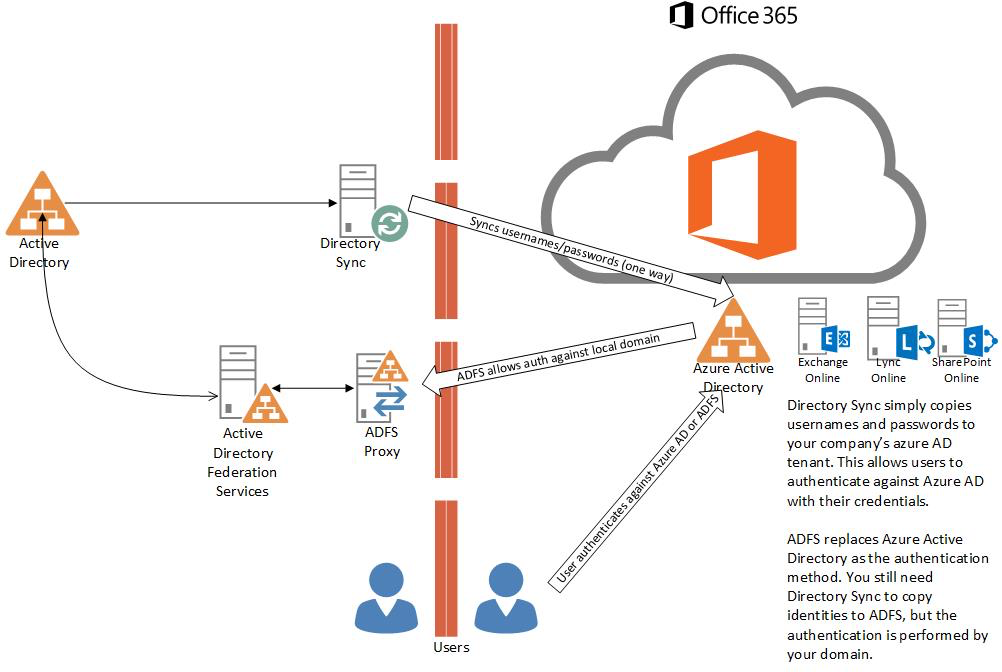
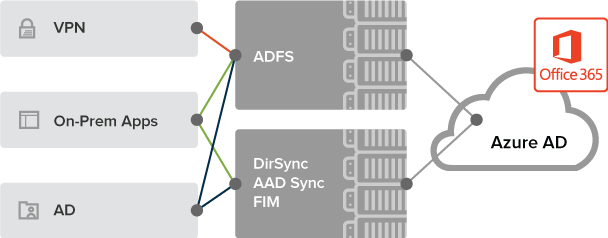
Active Directory Federation Services (ADFS)
Active Directory Federation Services V3 is now a Windows Role on Windows 2012 R2 and does not need to be downloaded separately as previously required. Active Directory Federation Services makes it possible to expose your Active Directory for Authentication purposes to the outside world. You might be asking “What about security?”. It is secured via SSL and exposed in most cases only via proxy server. ADFS also configures into a farm, which means that it can span across many servers for load balancing and redundancy purposes. To Office 365, ADFS offloads authentication back to your domain. This primarily used in single sign on scenarios, where you need your domain name to authenticate against. Office 365 doesn’t care about your actual domain per se when it comes to authenticating, it really only cares about your user name and password and will only authenticate UPN’s (user@domain.com). If you need to use single sign on and down level network names (domain\username) you will require ADFS.- Requires DirSync for synching Usernames and Password hashes
- Uses on-premise Active Directory for authentication
- It is critical for the enterprise once implemented, so having redundancy AKA a Farm and load balancing is recommended, which of course incurs additional cost
- It is absolutely necessary in order for SSO to work
</div> </div> </div> </div></div>
What if I told you there is another way to streamline the user account management without the need for ADFS and DirSync? Real-time synching, SSO and even gain additional capabilities such as app provisioning and management?
Enter The IMaaS (Identity Management As A Service) Era
Identity Management has evolved in fact. Companies such as Okta are providing solutions to clients who use services such as Office365 and streamline their user account management. Basically Okta is riding the O365 Success Wagon 🙂
Okta offers modern identity management for Office365.
Okta is a complete identity management product built as a single cloud-service and designed for both hybrid IT and cloud-first IT environments.
The Okta service provides
- single sign-on
- provisioning
- multi-factor authentication
- configurable security policy
- directory services and comprehensive reporting – all configured and managed from a single administrator console
The Microsoft Approach
Multiple Systems, On-prem and Cloud, Delayed Sync
The Okta Approach
Single System, Cloud-centric, Real-time
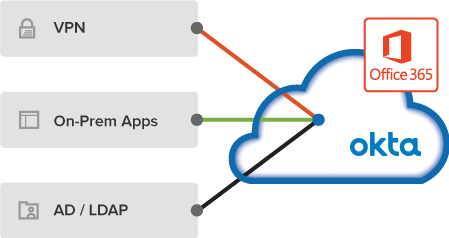
Identity management software has evolved over time. Previous generation software was built around periodic synchronization of data. Okta employs a much more modern, event-driven approach. This approach enables delegated authentication to AD at the moment a user attempts to log in. It also keeps user profile data in sync between on-prem AD and Office 365 the moment it changes.
</div> </div> </div> </div>
Another option now available to you, is Microsoft’s recently released Azure Active Directory Connect. Azure AD Connect makes it easy to integrate on-premise Active Directory, thereby providing your users a common identity across cloud and on-premise apps.
Some of the key Features/Benefits are:
- Companies can provide a common hybrid identity
- Admins can configure conditional access based on app resource, device and identity, network location
- Users use common identity to access cloud services such as O365 and third-party apps (ZendDesk, Quickbooks are good examples)
- Developers can leverage the common identity model and integrate their apps into Active Directory on-premise and Azure AD for cloud apps
</div>
</div> </div> </div> </div> </div></div>
There are trade-offs with any option you choose; are you ok spending on hardware or paying recurring monthly fees?
-Oscar